SafeConsole Platform
Complete USB endpoint protection to provision, manage, and audit
Maximize Security and Compliance with SafeConsole USB Endpoint Protection
SafeConsole USB endpoint protection platform provides comprehensive control over your organization’s USB security, offering a suite of modules designed to enhance data protection, endpoint security, and ease of management. Here are six key benefits of the SafeConsole platform:
Secure USB Device Management
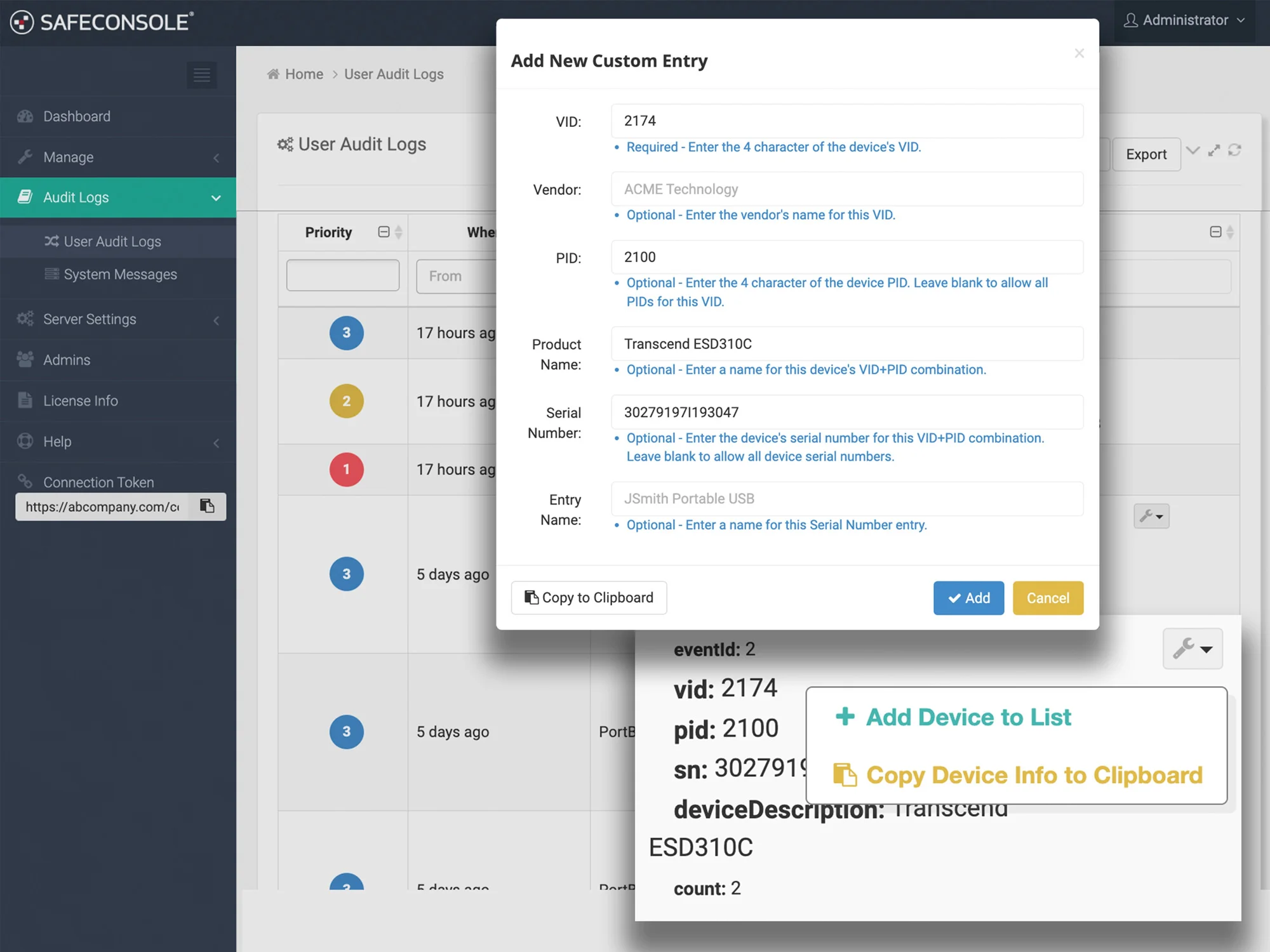
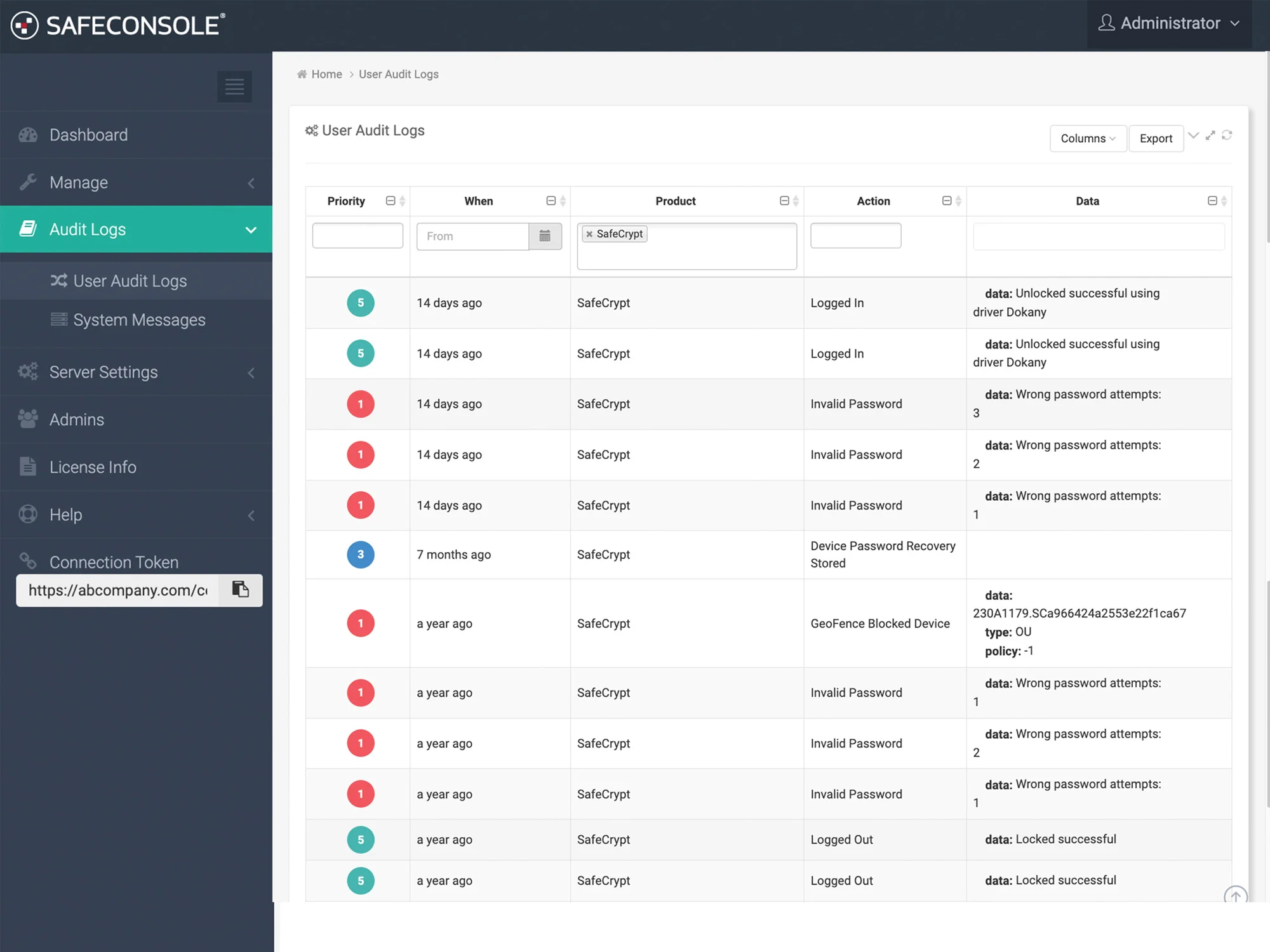
Remotely manage, configure, and audit encrypted USB drives, with options to lock or wipe devices if lost and enforce encryption policies for compliance.
USB Port Protection with PortBlocker
Ensure only authorized devices access USB ports, blocking unauthorized connections to prevent data leaks and malware threats.
Integrated USB Anti-Malware Protection
Trellix™ anti-malware scans files in real-time on SafeConsole-ready USB drives, automatically isolating and removing threats for safe data transfers.
SafeCrypt for Secure Cloud Storage
Encrypt files on local storage before uploading them to the cloud, providing end-to-end data protection across popular platforms like OneDrive and Dropbox.
Certified USB Data Erasure
Perform standards-aligned cryptographic erasure directly within SafeConsole to generate tamper-proof proof-of-erasure certificates, immutable audit logs, and centralized compliance reporting.
Flexible Cloud & On-Prem Deployment
Choose cloud deployment for speed, scalability, and compliant hosting, or on-prem for full control, sovereign compliance, and regulated-environment requirements.
SafeConsole Modules
SafeConsole’s flexible platform offers modular solutions that adapt to your organization’s specific security needs, all managed through a single, user-friendly web interface for complete USB endpoint protection.
- Secure USB Device Management: Provision, configure, manage, and audit encrypted USB drives remotely from anywhere. Learn More.
- USB Port Security: Control access at USB ports to prevent unauthorized transfers, ensure only approved devices connect, and strengthen Data Loss Prevention (DLP) and network security. Learn More.
- USB Anti-Malware Protection: Enable real-time scanning and quarantine for malware on USB devices, reducing the risk of threats and enhancing overall device security. Learn More.
- USB Certified Data Erasure: Certified, cryptographic erasure with automated proof-of-erasure, tamper-proof certificates, and NIST SP 800-88 compliance reporting. Learn More.
SafeConsole Platform Benefits
SafeConsole offers centralized control and security for USB device management, providing critical protections for data integrity and compliance across your organization.
- Modular Security Solutions: Choose from four modules that strengthen USB management and data protection.
- Web-Based Management: Easily control device policies and monitor compliance from a centralized platform.
- Scalable and Customizable: Configure solutions based on your organizational needs, enhancing USB security management.
Industry Use Cases
The DataLocker SafeConsole Platform serves as the perfect solution across multiple industries for USB endpoint protection:
Government Agencies
SafeConsole enables federal and local government organizations to securely manage encrypted USB drives, enforce data encryption policies, and control USB port access across endpoints. This ensures USB endpoint protection for compliance with strict regulations like FIPS, HIPAA, and GDPR while protecting sensitive government data from unauthorized access or loss.
Healthcare Organizations
Hospitals and healthcare providers use SafeConsole to securely store and transfer patient data on encrypted USB drives while maintaining HIPAA compliance. With features like anti-malware scanning and remote drive wiping, organizations can ensure data integrity and security during telehealth sessions and internal transfers.
Financial Services
Financial institutions leverage SafeConsole for secure data handling across distributed teams. The platform’s port control and audit capabilities prevent unauthorized USB usage and track file movements, helping organizations meet PCI-DSS compliance while safeguarding sensitive customer and financial information.
Educational Institutions
Universities and research facilities utilize SafeConsole to manage secure USB drives for storing confidential research data, preventing unauthorized USB device access, and mitigating malware risks. The platform’s modular design allows schools to scale security features based on their evolving needs.
Enterprise Businesses
Corporate organizations adopt SafeConsole to maintain endpoint security, especially in hybrid or remote work environments. The platform ensures secure collaboration with encrypted USB drives, blocks unauthorized devices through PortBlocker, and provides administrators with centralized control over device policies and usage.
Defense Contractors
Defense contractors rely on SafeConsole’s on-premises deployment option to maintain full control over data security. With features like geofencing, remote wiping, and detailed auditing, the platform ensures secure handling of classified data in compliance with military-grade security standards.
Trusted by

Customer Testimonials for SafeConsole
Compare SafeConsole Plans
Choose the right level of USB endpoint protection and management for your organization.
Basic Plan
For organizations seeking fundamental USB device management and data security. SafeConsole Basic offers core protection with essential features like password policies, device inventory tracking, and basic auditing.
- Security Features: Establish strong baseline security with password enforcement and remote reset capabilities.
- Device Inventory: Maintain an automatic directory of all users and devices for easy tracking.
- Auditing: Track essential device actions and file movements for compliance.
Professsional Plan
SafeConsole Professional builds on the basics by adding premium priority support and the ability to do advanced hardware replacement RMAs for managed devices to meet the needs of growing organizations.
Everything in the Basic Plan, plus:
- Premium & Priority Support: Gain access to dedicated, fast-track customer support, ensuring timely resolutions and expert assistance.
- Advanced Hardware Replacement: Minimize downtime with expedited RMA services, offering immediate hardware replacement for defective devices to keep your operations running smoothly.
Enterprise Plan
This plan is designed for customers with integration requirements. SafeConsole Enterprise includes all Professional features and adds seamless integration with existing systems.
Everything in the Professional Plan, plus:
- API, SIEM Integration & SSO: Seamless integration with security systems for enhanced monitoring and admin convenience.
- Custom Geographic Cloud Server Options: Tailor server locations for compliance with regional data security requirements.
Frequently Asked Questions (FAQ)
What are theSystem Requirements for using SafeConsole?
It depends on your deployment method:
-
SafeConsole Cloud:
No system requirements. The platform is fully managed by DataLocker and accessed via a web browser. There’s no local installation or server setup needed. -
SafeConsole On-Premise:
If deploying SafeConsole on your own infrastructure, your server must meet the following minimum system requirements:-
Processor: 2 Core CPU
-
Memory: 4 GB RAM
-
Storage: 100 GB of available drive space
-
Operating System: 64-bit Windows OS (Windows 10+ or Windows Server 2016+)
-
What is SafeConsole Secure USB Device Management?
SafeConsole Secure USB Device Management allows organizations to remotely manage, provision, and audit their fleet of encrypted USB drives, ensuring full control over data security.
How does SafeConsole PortBlocker prevent data loss?
SafeConsole PortBlocker ensures that only approved USB devices can connect to workstations, preventing unauthorized data transfers or malware intrusions via USB ports.
Can SafeConsole protect my USB devices from malware?
Yes, SafeConsole’s Antimalware module scans files in real-time using Trellix™ Enterprise Anti-Malware, detecting and removing threats before they can harm your network.
What cloud storage providers are compatible with SafeCrypt?
SafeConsole SafeCrypt works with popular cloud storage providers, including Google Drive, Dropbox, and OneDrive, encrypting files locally before they are uploaded.
Is SafeConsole available as an on-prem solution?
Yes, SafeConsole can be deployed as an on-prem solution on your dedicated server, providing complete control over your USB device security management and USB endpoint protection.