Preparing for Your CMMC Audit
Organizations seeking Cybersecurity Maturity Model Certification must make sure their company is 100% ready for certification before they begin the certification process, or they will fail their audits. Assessment guides are available to help walk organizations through the process. Still, they’ll want to make sure they fully understand not only what the requirements mean but how to execute the processes and practices effectively and with evidence.
Should Your Business Do It In-House or Work With a CMMC Consultant?
Large DoD contractors are likely to have an IT staff and resources dedicated to security, with the ability to meet appropriate CMMC levels of cybersecurity in-house.
Smaller DoD contractors should consider outsourcing to a consulting partner with appropriate expertise to help their company become compliant. DoD contractors are responsible for ensuring their company meets applicable cybersecurity requirements, so it’s essential to choose a reputable provider. The CMMC-AB Marketplace is a great place to locate Certified Third-Party Assessor Organization’s (C3PAOs) and consulting partners.

Where Is a Good Place to Start?
Perform a Gap Analysis
Gap analyses determine how close the contractor is to being fully compliant and the areas that need improvement. An essential first step is to identify the Controlled Unclassified Information (CUI) within an organization.

For the companies following the NIST SP 800-171, this process should be straightforward. The CMMC will cover the items listed in the NIST SP 800-171 but will also have additional requirements depending on the CMMC certification level required.
What are Auditors Looking For?
Think of an audit as a zoomed-in look at one of the processes in an organization, such as looking at your IT security posture. There are many areas auditors might look at depending on the CMMC Level the organization is trying to obtain. They can look at areas like payroll or learning the HR processes. Essentially, it’s a deep test of one of the processes within an organization’s environment.
How Do Organizations Prove What Auditors Are Looking For?
In CMMC, there’s a lot of talk around evidence, but what is considered CMMC evidence? What is it used for, and how is it collected?
When an auditor comes into an organization and engages with an employee on a specific policy, they will need an example of how that policy is executed. The example is generally the evidence and could be a photo, a screenshot from a console, or maybe a log repository. There are also times when evidence is needed from a process, and it can come in a wide range of forms.
Make The Auditors Jobs Easy
Depending on the organization’s size, the average time frame the audit will take is between 1.5-3 months, so you’ll want to make this process as smooth as possible.
The first thing the auditors will evaluate is the environment:
- How many servers are there?
- How many workstations?
- What does it physically look like? Is it big or small? – if it’s big, it will increase the load and timeline of engagement with an auditor.
Before they get started, auditors need to understand precisely what they need to evaluate. Organizations should map the controls to their environments for all in-scope systems like workstations, servers, etc. Time and date stamps are necessary; auditors need to see the evidence they are being presented isn’t from a year ago.
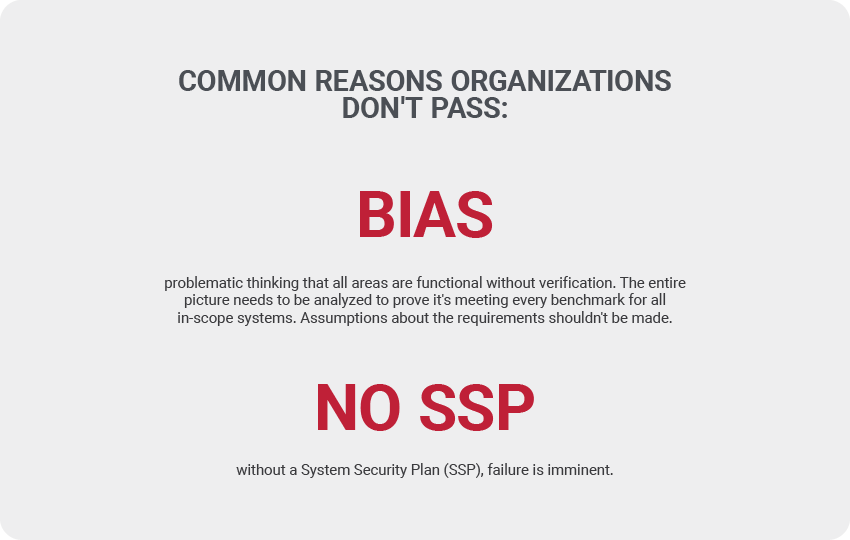
Once they understand the environment, they’ll dig into policies, procedures, and everything is written down. If something isn’t written down, they’ll need to know why and what is being done. Keep in mind that all areas of requirements will need tangible policies the auditors can review, and you should anticipate anything they are going to want. This is usually in the Security System Plan (SSP), and organizations without SSPs will not pass their audit.
When Organizations Don’t Pass
The biggest challenge of this certification is that it has many requirements that all need to be proven to work effectively. When organizations are not compliant, the auditors will let them know the areas they need to improve, but they will not help them solve the problems. The organizations will need to hire a remediator to help them get the problems solved. They can confirm if a solution will work for compliance by reviewing things like log repositories and can also help to vet vendors.
When it comes to CMMC, the sooner organizations meet the requirements; the more accessible certification will be. It’s important to remember the many resources and services available to assist with this transition. For more information on CMMC and other cybersecurity information, make sure to follow us.