Suppose you were to visit the break room of one of the vendors for the Department of Defense. In that case, chances are that the government’s new Cybersecurity Maturity Model Certification (CMMC) compliance standard is a water-cooler hot topic. Still, there’s a lot of confusion surrounding it, primarily because the folds and kinks are in the ironing stage, leaving many businesses feeling uncertain about where to begin in the process.
Why Is CMMC Compliance Needed?
The CMMC was designed to protect controlled unclassified information, or CUI, throughout the defense supply chain and represents a significant shift in DOD policy. In the past, vendors were able to self-certify that they were meeting the requirement of NIST 800-171. Unfortunately, due to the rapid increase in cybercrime, this didn’t work out so well, and the government determined the need for third-party verification.

Where Do You Start?
The first and most crucial step is to determine if your business has the skill set, expertise, experience, and bandwidth to tackle this type of certification process alone or if you’ll need help. The process will be less cumbersome for some companies, while others need to prepare themselves for a thorough and heavy lift. Be honest with yourself because you don’t want to go into this unprepared.
To determine CMMC requirements for your business, and if you need help, you first need to evaluate a few things, also known as scoping.
Begin Gathering Information
Do you handle any type of government contracts?
No – You may still be required to get CMMC certified if you are a supplier for a DOD contractor that works with CUI. If your customer has to provide access to CUI to you to complete your work then you will need to be certified to the level that matches the CUI. If you only provide a Commercial Off the Shelve (COTS) product then you would not need to be CMMC certified as no data would be transferred to you for the development or use of your product.
Yes – you will need to be compliant, but there are different types of requirements depending on what level of certification you need
What types of systems and networks do you use?
Make a detailed list of each, including how and where they’re used.
Do you have the following protocols in place?
- Hardware device inventory
- Devices connected to the company’s network
- Employee cybersecurity training
- Employee code of conduct contract
- System access trackers
- System access controls
- Password management
- Incident response
- System security plan
Next, determine how many employees you have, what things they have access to, and what protocols and procedures are in place for them.
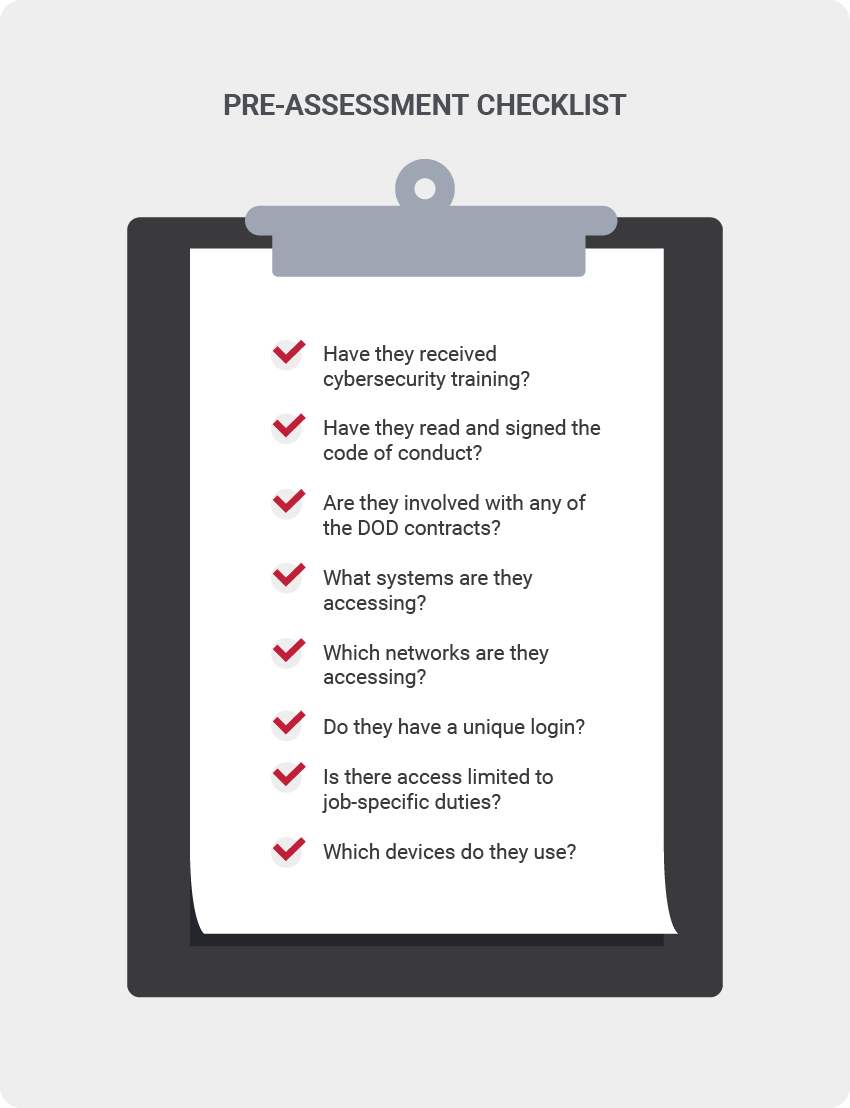
By asking these questions, you’ll have data on:
- Device inventory
- Which employees are involved with government contracts
- Who has/hasn’t received security training,
- Software application logs
- Access control logs
- Network access logs
- Passwords
Have An End Result In Mind
A best practice to follow in the beginning is to map out the entire certification process to understand the end goal. The only way to know how thorough your certification process will be is to know what level of certification your business needs to achieve. There are a few things you can do in the meantime to get you up to speed.
One place to start is to access any previous DFARS submission so you can begin to review your SSP, POA&M, and SPRS score of the prior submission. These can act as a foundation to help you determine what you will need to do with CMMC compliance.
I Know My Level, Now What?
Once your initial assessment is complete, you’ll want to get your executive team on board, as well as any other stakeholders of the company involved. Together you can review where you’re at and determine if this certification is right for your business. You’ll want to make sure there’s enough future business projected with the DOD to ensure the time, money, and energy invested into CMMC compliance is worth it. If it isn’t, stop pursuing it. If it is, which is a promising scenario, then make sure your team is on board.
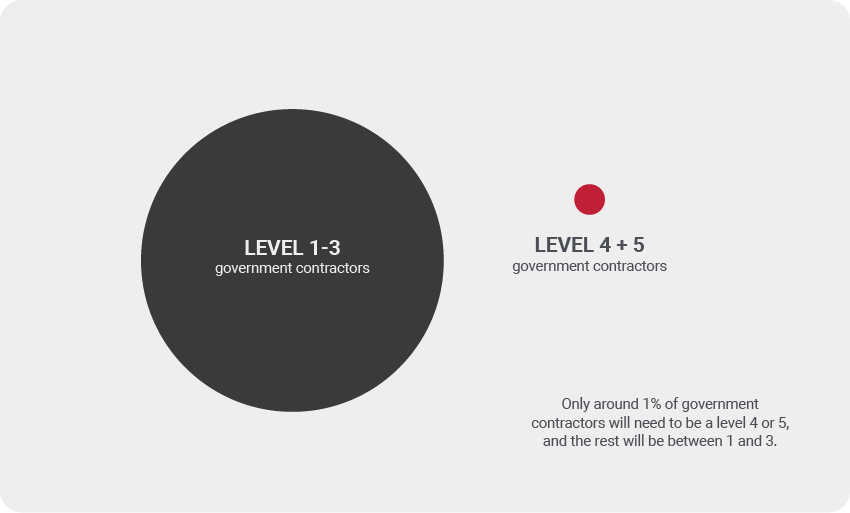
A quick note of consideration on the levels: there are 17 different domains covered under the five CMMC maturity levels. Only around 1% of government contractors will need to be a level 4 or 5, and the rest will be between 1 and 3. Each level has specific requirements known as domains. Domains are how the security controls are grouped. In level 1, there are only 17 controls, but in level 2, there are an additional 55 controls, not to mention additional required security practices. As each level increases, so do the required control and practices within the domains.
As for the 17 domains, just one of those is physical security, such as the company’s building, and the next is personnel security, and so on. Generally, the people that handle physical security and personnel security are not in the IT department. You’ll want to confirm scope and boundaries with your executive team about which parts of your business require certification. Together you’ll need to agree on the timeline as well as the resources you’ll need to achieve compliance. Once you determine this, you’re now ready to start the bulk majority of the work.
CMMC certification information is found on The Office of the Under Secretary of Defense for Acquisition and Sustainment website. Here you can find assessment guides, updates, or you can contact them directly for assistance.
Sources
https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-172.pdf
https://cmmcab.org/marketplace/
https://www.acq.osd.mil/cmmc/docs/CMMC_ModelMain_V1.02_20200318.pdf
https://www.ic3.gov/Media/PDF/AnnualReport/2020_IC3Report.pdf
https://www.acquisition.gov/dfars
https://www.acq.osd.mil/cmmc/contact-us.html