CMMC is one of the most important compliance standards to come along in the modern digital age. One could argue that is among the most complex as well. The DOD is demanding contractors to endure a rigid assessment process that technically, has never been conducted before. What’s more, CMMC is very much a work in process. Some of the specifics are currently being formalized in the federal rulemaking process, while training courses are being provided to ensure the program can field a serviceable number of assessment and certification professionals.
The book on CMMC is still being written. That said, optimal preparation is invaluable. This section will cover the groundwork to make sure you’re ready for the audit process.
Tend to Your Data Environment
The first task on the agenda is taking an exhaustive look at your IT environment. You need to determine which sets of data are relevant to the CMMC scope, as well as the systems responsible for processing, transmitting, and storing that information.
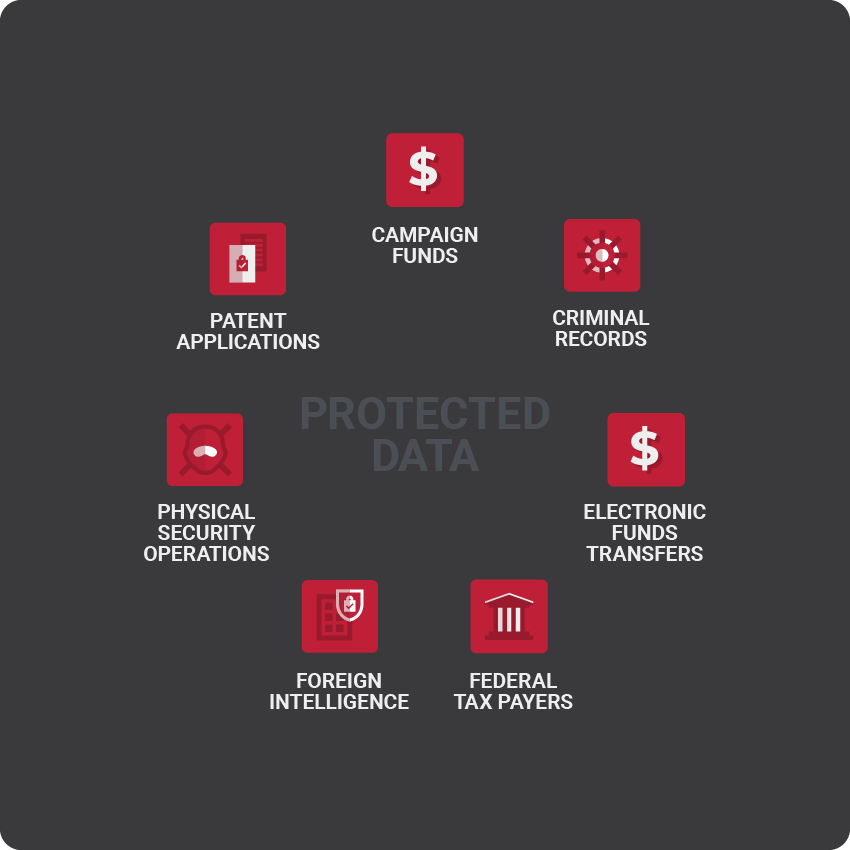
The protected data or CUI, covers a broad range of information, including IT assets related to the following areas:
- Campaign funds
- Criminal records
- Electronic funds transfers
- Federal tax payers
- Foreign intelligence
- Physical security operations
- Patent applications
While CMMC prioritizes confidential information in non-government systems, contractors may possess data that intersects with existing government data at various points across their infrastructure. Careful analysis of your environment will go a long way in setting the tone for a relatively clean audit procedure.
Follow Established Roadmaps
There is no single silver bullet to ensure impenetrable cyber security. As such, guidelines tend to share characteristics from one compliance standard to the next. Contractors targeting CMMC certification would be wise to consider how and what they can borrow from existing compliance standards. The most obvious example is the framework CMMC is designed to usurp — NIST SP 800-171. Although the standard left plenty to be desired in the way of uniformity, NIST SP 800-171 provides specific guidelines for handling CUI in non-government systems, which is the basis of CMMC.
Implementing security measures culled from NIST SP 800-171 or other regulatory standards will not guarantee CMMC compliance. However, the practices preached in those programs may very well ease the transition along the road to certification. Take the time to review any existing compliance programs with potentially reciprocal criteria. At the very least, the knowledge gleaned from those assessments can give you a better understanding of the CMMC auditing process.
Assess Your Preparedness
Considering the sensitivity of government business, there’s a great chance that DOD contractors have already implemented many of the essential security measures CMMC certification requires. Nevertheless, it’s vital to understand your level of preparedness before heading into an audit.
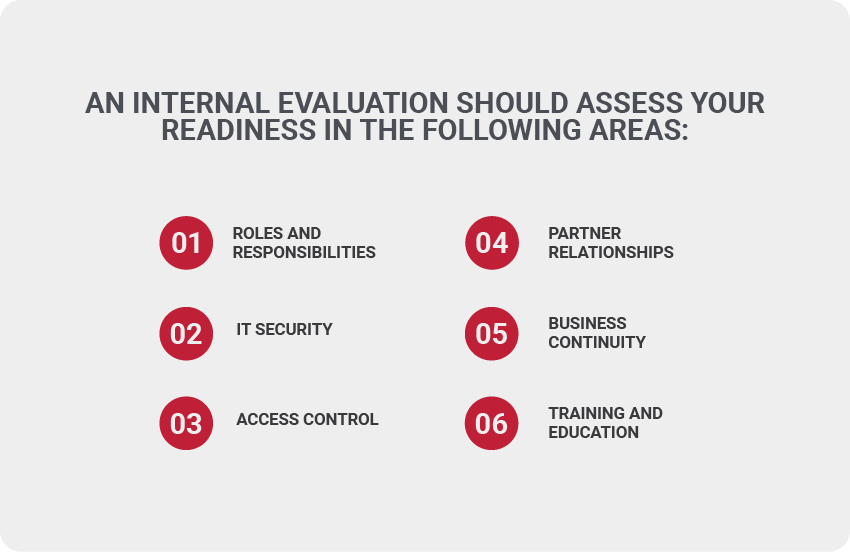
An internal evaluation should assess your readiness in the following areas:
Roles and responsibilities: Who manages IT security in your organization? Is senior management involved in the process? If so, to what degree? How often does IT security personnel assess your level of risk?
IT security: How does your IT security team monitor the network to detect and remediate potential vulnerabilities? What controls have been implemented to protect the environment in the event that threats are detected?
Access control: Who has access to CUI across your organization? What measures have been taken to prevent unauthorized access to that data and the systems that house it?
Partner relationships: How do vendor relationships potentially impact your compliance status? Are those partners accounted for in your risk assessment strategy?
Business continuity: Is your company equipped to recover from a security incident or natural disaster? How often is that response plan tested?
Training and education: Does staff understand the security measures implemented to protect the network? Are they actually following the protocols and procedures set in place?
The process of accessing your preparedness should be as extensive as the audit for CMMC certification. Due to the detailed nature it demands, it is advisable to consider bringing in a third-party firm to perform an assessment of the IT environment. An impartial evaluation will help to ensure that you’re ready for the official audit by providing an honest assessment of your cyber security prowess.
Address Identified Problems
The cyber security threat landscape is constantly evolving. Systems that are secure today, might be outdated and vulnerable to new attacks tomorrow. If the assessment yields problem areas that warrant attention, initiative must be taken to remediate them and bring the organization closer to compliance. Filling security holes often calls for additional investments, so it makes sense to estimate what it will cost to address each gap uncovered in the assessment.
Although the cost of CMMC audits may be redeemable after receiving certification and subsequent contract awards, the same cannot be said for the resources you shell out to get there. Consider it money well spent. This is now the price of doing business with the Defense Department, and the cost of non-compliance is more than any contractor is willing to wager.
No Time Like the Present
Recognizing the challenge at hand, the DOD introduced CMMC as a five-year rollout that would give contractors ample time to adapt to the program. Organizations can stay ahead of the curve by making audit preparations as soon as possible. This proactive approach will better assure that you are compliant well before the final deadline rolls around.