Any system administrator understands the value of a comprehensive data recovery plan. That importance has increased significantly in the era of ransomware, where ambitious cyber criminals are aiming to hit unsuspecting organizations where it hurts the most―—in their pockets.
Unfortunately, there is no one silver bullet capable of thwarting this destructive menace. However, there are a number of tools that can be effectively wielded in the fight. And believe it or not, your everyday USB drive is among them.

Say What?!
Just about everyone is familiar with flash-based USB drives. Known for their portability, these small devices have long provided an easy way to store and transfer data of varying capacities. While they are commonly used for simple tasks, USB drives have the potential to play a much more significant role in your data protection strategy. The basis of that promise lies in its ability to simulate the critical function necessary to boot and run entire IT systems.
In the not so distant past, the job of booting a computer was reserved for CD and DVD media, which contained the operating system as well as the files required to execute both the OS and corresponding programs. Surely, everyone remembers a time when you couldn’t install Windows, or Mac OS X without one of these discs―—and how they seemed to magically disappear whenever you needed to reinstall the system.
Innovations in flash storage eventually made it possible to pack those same functions onto a USB drive. Nowadays, USB drives can act as self-contained operating systems or tools that round out a multi-layered data protection strategy.
The USB Advantage
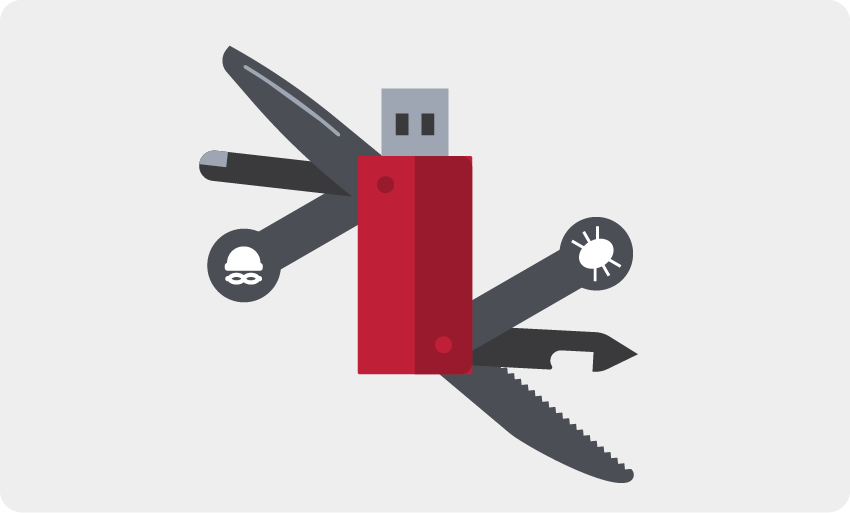
Though it’s not ideal on first glance, a USB drive is fully capable of protecting your data against malware and other security threats. When it comes to ransomware protection, these handy devices offer a number of distinct advantages:
1. Cost effectiveness: Flash drives are downright cheap. Of course, the actual price depends on factors such as capacity, quality, and brand name, but you can typically secure something reliable without even remotely breaking the bank.
2. Convenient size: Between documents, photos, and videos, the amount of data on your systems can quickly lead to an untenable storage situation. Flash storage makes it possible to fit multiple terabytes of data in the palm of your hand. If capacity is an issue in your data protection scheme, a USB drive can provide tremendous value to the cause.
3. Robust performance: The “flash” component of a USB drive is the chip-based memory it uses for storage. By nature, this composition enables fast speeds, easy rewriting, and non-volatility that allows it to retain data with or without power. What’s more, the lack of moving parts creates a degree of durability that makes USB drives less susceptible to physical damage.
4. Ready for recovery: USB drives are random access devices. In essence, that means you can restore specific files by simply browsing the device and copying them to your preferred destination. This process is far more cumbersome in a traditional backup system, which may require you to rewind and play hours of tape to find the information you need.
Weaponized for Data Recovery
The potential of USB drives is not lost on the cyber security industry. A growing number of vendors provide customers with tools that allow them to recover their data from compromised systems. These toolkits can be easily installed onto a USB drive, where they may then be used to scan the infected machine and remove any malware detected. The beauty of such a configuration is the ability to perform the aforementioned maintenance offline, in a safe environment. That means you can rescue your system without fear of executing the malicious code at the root of the ransomware attack.
Disaster can strike at any time, and when it does, the weapons in your data protection strategy could make all the difference in your ability to rebound. USB drives are more than capable of playing a role in your ransomware protection strategy. The key to maximizing their effectiveness is understanding the limitations, and recognizing exactly how they can benefit the data recovery process.
For more information about how to enhance USB port and USB drive security, check out SafeConsole for centralized USB drive management and PortBlocker for an easy way to remotely manage USB ports.